
Cybersecurity services for software and embedded products
Raising cyber resilience for your products and ensuring your compliance needs
With the introduction and continuous expansion of the Internet of Things (IoT), the world becomes more and more connected. The combination of “smart” devices, mobile or web applications used to interact with them and cloud services allowing them to connect with each other lead to the development of overlapped IoT ecosystems.
Moreover, as the IoT has long ago passed the barriers of consumer products, organizations are making use of such products and solutions, making them an integral part of the ecosystem. In the ecosystem of IoT, manufacturers of products hold one of the most important roles: they are ultimately the ones that decide which features will be included in their products.
Historically, the world of IoT has been driven by functionality in the past years. The products with the most and more revolutionary features got an edge over their competition. Recently, the aspect of cybersecurity in IoT has become a topic that cannot be ignored. Moreover, we are at the point when cybersecurity issues associated with these products are not theoretical anymore and can very likely happen with the products that we use in our daily life. Scaling up this idea to the fact that what we call today IoT is not anymore linked fully to smart gadgets, but also includes vehicles, medical devices, industrial and telecommunication equipment, and more, gives the perspective of how critical a cybersecurity attack can prove to be.

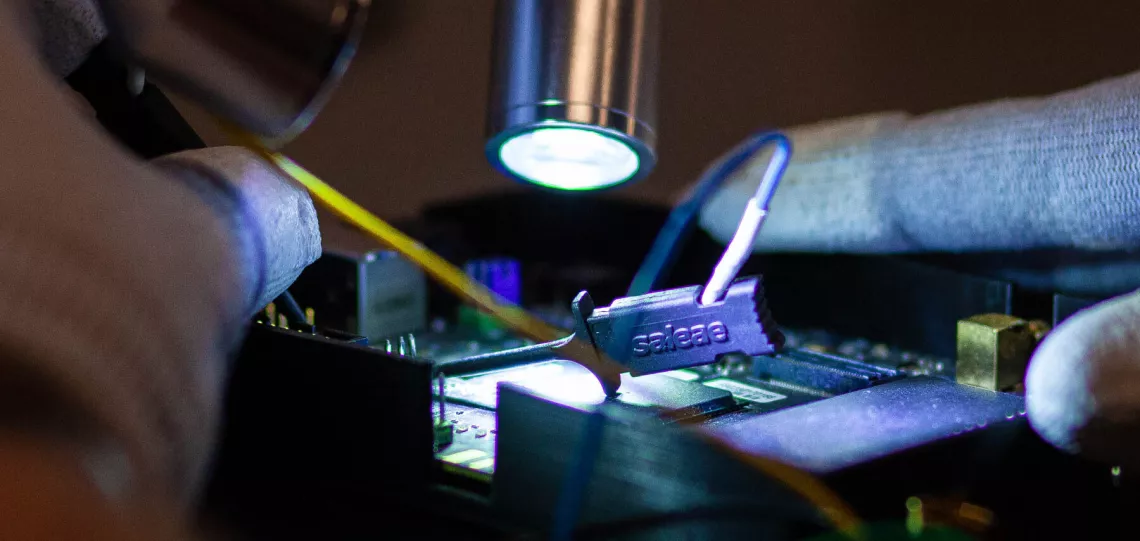
Cyber Expertise in IoT

Cyber Services tailored to product manufacturers

People, Process and Technology integrated
Our services for your different products and systems
Securing the IoT Domain
Securing the IoT Domain
For a long time, the IoT domain lacked clear standards and frameworks to help manufacturers build security into their products. Now, that time is over. Currently, there are many internationally recognized standards, frameworks, and certification programs. These resources aid manufacturers in choosing the right security features for their products.
Several standards stand out in this field.
- The IEC 62443 series is the go-to standard for industrial cybersecurity, including components and systems.
- For medical devices, UL 2900 is the reference standard.
- The ETSI EN 303 645 standard, recently completed, is the main reference for consumer IoT products.
- Additionally, ISO 21434 is gaining recognition as an essential standard for cybersecurity processes in connected vehicles.
Support and Preparation
The road to product compliance (in line with a standard or regulation) starts with careful preparation. In some cases, for example for vehicles development, manufacturers need to focus strongly on how to meet all the applicable regulatory requirements from an early phase, to ensure that the vehicles can be afterwards placed on the market. The same applies to medical devices, which are also regulated from a security perspective. At the same time, Secura can support manufacturers with design reviews or recommendations to achieve compliance to a certain standard for products such as consumer IoT, network components or industrial products. Finally, preparation for an international certification program such as Common Criteria or IEC 62443 can be offered to interested manufacturers.
Compliance
One of the most effective ways to improve market recognition and demonstrate a good security posture is demonstrating the product's compliance with the relevant international standards. Secura can support testing and compliance services in line with multiple standards, applicable for specific types of products. IEC 62443 testing and compliance can considerably increase the market recognition for industrial products, while UL 2900 compliance is a strong start for medical devices. In the world of consumer products, standards such as ETSI EN 303 645 or IoT Security Foundation can be used as a very good baseline for testing. Finally, the ISO 21434 standard for automotive cybersecurity management systems is a highly recognized standard that vehicle and components manufacturers can seek compliance with.
Certification
Official certification is ultimately the most important recognition that a product can achieve. It means that the product's security is backed not only by a test report but by an accredited organization or government that has reviewed and approved the results of the test report. There are multiple certification programs that Secura can support manufacturers with, depending on the type of product. Common Criteria is the most internationally recognized security certification scheme, allowing international product recognition and easier access to local governments or large-scale asset owners. Locally in the Netherlands, Secura is one of the few labs that can support the BSPA evaluation, which is seen as a light version of Common Criteria. Secura can support vehicle manufacturers in the process of obtaining an official type approval based on the UNECE regulations on Cybersecurity (R155) and Software Updates (R156). Finally, industrial systems and components can obtain their certification based on the IECEE scheme (based on IEC 62443), while consumer IoT products can be certified based on ETSI EN 303 645.
More Information
Would you like to learn more about our cybersecurity services for your products? Please fill out the form below and we will contact you within one business day.

ABOUT SECURA
Secura is a leading cybersecurity expert. Our customers range from government and healthcare to finance and industry worldwide. Secura offers technical services, such as vulnerability assessments, penetration testing and red teaming. We also provide certification for IoT and industrial environments, as well as audits, forensic services and awareness training. Our goal is to raise your cyber resilience.
Secura is a Bureau Veritas company. Bureau Veritas (BV) is a publicly listed company specialized in testing, inspection and certification. BV was founded in 1828, has over 80.000 employees and is active in 140 countries. Secura is the cornerstone of the cybersecurity strategy of Bureau Veritas.
Waarom kiezen voor Secura | Bureau Veritas
Het doel van Secura/Bureau Veritas is om uw vertrouwde partner in cybersecurity te zijn. Wij gaan verder dan snelle oplossingen en geïsoleerde diensten. Onze geïntegreerde aanpak zorgt ervoor dat elk aspect van uw bedrijf of organisatie cyberweerbaar is, van uw technologie tot uw processen en uw mensen.
Secura is de cybersecuritydivisie van Bureau Veritas, gespecialiseerd in testing, inspection en certification. Bureau Veritas werd opgericht in 1828, heeft meer dan 80.000 werknemers en is actief in 140 landen.





