FROM MATTRESSES TO ARTIFICIAL HEARTS: WHY IOT SECURITY IS CRUCIAL
Author: Liesbeth Sparks
IoT devices are everywhere: there are billions of devices connected to the internet. But how safe are they? The exact risks depend on the functionality of a device. But in extreme cases IoT security can be a matter of life and death, says Jasper Nota, Senior Security Specialist at Secura.
Nota knows this is true, because he tested the security of an artificial heart. In this article he explains why IoT security is so crucial. He also discusses what can happen if IoT devices are breached, and which steps product manufacturers and users can take to secure their IoT devices.
THE RISKS OF POOR IOT SECURITY
There are all kinds of risks when it comes to IoT security. If an attacker manages to hack a smart device, the consequences can be serious, says Nota: ‘Of course, the exact security risk depends on the environment of the product and what the product is used for. The risks for a smart mattress, for example, are completely different than for devices used in an operating theater.’
But even though the risks vary per device, a lot of devices can cause harm if they are not secure, says Nota: ‘What would happen if an attacker can blow up the battery of a device? Who can an attacker spy on if the product has a camera inside? These are only a few examples of elements in a smart device that can be used to cause harm.’
STEALING DATA THROUGH A FISH TANK
One famous example of harm caused by an insecure IoT-device is the case of the casino fish tank. In 2017, a US casino installed a smart aquarium with sensors that monitored the temperature of the water. These sensors were connected to the casino’s network. Cybercriminals managed to penetrate the network through the fish tank and stole 10 gigabytes of data.
I realize that if I was able to find a weakness, a malicious actor is probably capable of finding it as well. ~ Jasper Nota
INCORPORATED IN A BOTNET
‘Another real danger is that an insecure device can be incorporated in a botnet’, warns Nota. ‘A botnet is a group of devices taken over via a particular vulnerability or misconfiguration. That allows a malicious actor to control those devices. Using a botnet, an attacker can carry out all kinds of attacks.’ For example: perform DDoS attacks or steal sensitive data from the network the device is a part of.
A digitally insecure device can harm users. But the dangers are real for device manufacturers as well. Security issues in products can lead to reputational damage and a drop in market value of the company.
HOW TO MAKE YOUR IOT PRODUCTS MORE SECURE
What can you do to maximize the security of IoT products, as a manufacturer? ‘Ideally, a manufacturer will involve security experts during the design phase of a product’, says Nota. Of course, if the product is already on the market, that’s not possible.
There are a few security measures that are relatively easy to implement before a product goes to market, according to Nota: ‘Make sure not every device has the same default password. Also: make sure the software in the device can be updated. That way any security flaws you discover can be patched.’
For users, it’s important that they make sure IoT devices are isolated from each other and the rest of the network.
FROM HEADSETS TO DOOR LOCKS
Of course, another way to secure IoT devices, is to have them tested by security specialists like Nota, so that you can fix any vulnerabilities before a malicious actor can exploit them. Nota primarily tests the digital security of consumer electronics and medical devices at Secura.
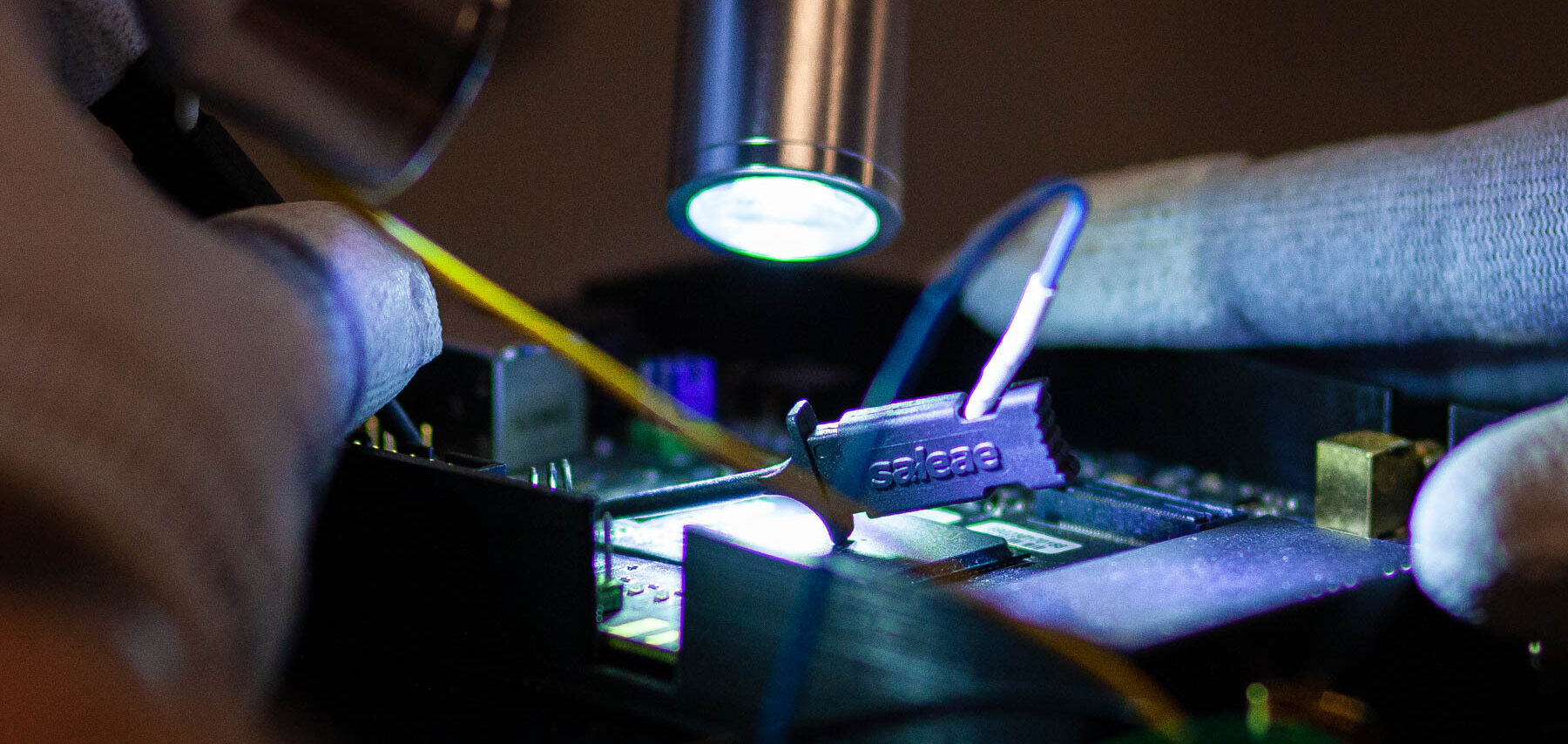
‘Over my career I have tested a lot of unique devices. Smart pills, for example. But also applications that run on mixed reality headsets, a smart mattress, smart door locks, alarm systems, televisions, smart watches and muscle stimulators, to name a few. Most devices are physically sent to our testing lab at the Amsterdam office.’

Slimme apparaten testen op kantoor in Amsterdam
TESTING AN ARTIFICIAL HEART
‘The most interesting product I’ve tested so far was an artificial heart. That was interesting because it’s really about human life. I can’t go into too many details about the research itself. But we discovered that the heart’s security was well designed. There were several layers of security; what we call ‘defense in depth’. However, in the end we did discover several vulnerabilities that could have had a catastrophic impact on the patient’s life.’
ADRENALINE AND ANXIOUSNESS
What does it feel like to find serious weaknesses in products? Nota: ‘It gives me mixed feelings. As a hacker, I get a real adrenaline rush when I find severe vulnerabilities. On the other hand, it makes me a bit anxious sometimes. A malicious actor probably has more time on their hands to find weaknesses.’
IoT | Testing & Certification‘I realize that if I was able to find a weakness, a malicious actor is probably capable of finding it as well. But I’m glad I can report these issues in the work I do. And I see that vulnerabilities are mitigated. So that’s satisfying.’
NEW EU REGULATION FOR IOT
Now is a perfect time to work on the security of your IoT products, because in August of 2024 an addition on the EU Radio Equipment Directive (RED) will come into force. Nota: ‘This means any IoT product brought onto the European market will have to have minimal security requirements.’ The EU is also working on even more far reaching regulation: the Cyber Resilience Act (CRA).
From a security point of view, these new laws are good news, says Nota: ‘The problem we currently face, is that the more a product manufacturer invests in security, the more expensive the product becomes. At the moment this means that secure devices are less competitive in price than insecure devices.’
‘Because many consumers can’t tell the difference between a secure and an insecure product, this means the secure product loses. These new laws will raise the bar for everybody, creating a more level paying field.’
CONCLUSION
IoT security is critical, both for product manufacturers and the users of these devices. By prioritizing security product manufacturers can make sure their customers aren’t harmed, and can prevent all kinds of damage to their own business as well.
MORE INFORMATION
Do you want your smart IoT-products tested? Or do you want to learn more about our cybersecurity services for IoT-technology? Please fill out the form below, and we will contact you within one business day.






