Cloud services are becoming increasingly popular, so audits and pentesting of cloud environments are also becoming more and more in demand. Security analysts need to have other skills to do these audits/tests. Many courses are available, but they lack the in-depth knowledge to understand the services fully. That is why Secura developed the BrokenAzure.Cloud tool.
Secura Develops 'BrokenAzure.Cloud', a CTF Tool to Test Azure Cloud Knowledge
The Growing Need for Cloud Security Analysts
Traditional on-premises solutions and hardware are more often being replaced with cloud (native) services. This has the advantages of not having to maintain hardware, low entry costs, and virtually unlimited scalability. As this interest in cloud infrastructures increases, cloud security becomes an even more important topic.
Companies request more and more security audits and penetration tests on their cloud environments to ensure that cloud infrastructures are configured correctly and securely. Cloud and on-premises infrastructures are quite dissimilar, so security analysts require different skills when auditing a cloud infrastructure. Several courses and exams are available to learn how to work with and audit cloud environments. All these courses teach students a global understanding of cloud security. However, they often miss the in-depth knowledge required to understand and secure services fully.
Two cloud experts and trainers at Secura, Ricardo Sanchez and Roy Stultiens, wanted to close this gap by developing an intentionally vulnerable cloud environment, BrokenAzure.Cloud. As Secura wants to give opportunities to young talent to do research and develop new skills, this project was turned into an internship project for Fontys University of Applied Sciences ICT & Cyber Security student Siebren Kraak. This online CTF tool, which he developed, is available 24/7 and does not need to be set up on requests when someone would like to use it
Research Goal
This project aimed to research how a CTF-like tool can be built that gives Secura the ability to test and improve the Azure cloud knowledge of (cloud) security analysts. The tool should have multiple challenges that consist of common misconfigurations in the Azure cloud space. Preferably, his tool will be hosted on the internet so everyone can use it. One challenge is creating a contained, vulnerable application where only the expected attack chain can be exploited.
Eventually, the final research question is, 'How can a simulated environment be created that tests and improves the Azure cloud hacking knowledge of cyber security professionals?'
The infrastructure-as-code language Terraform was used to make sure that the project is easily maintainable and that there is version control on the infrastructure.
Researching Common Vulnerabilities
Just like software, network infrastructures commonly share misconfigurations that cause security issues. The challenges will be based on common Azure misconfigurations to ensure the CTF tool is as relevant as possible. The table below summarizes the most common misconfigurations in Azure environments.
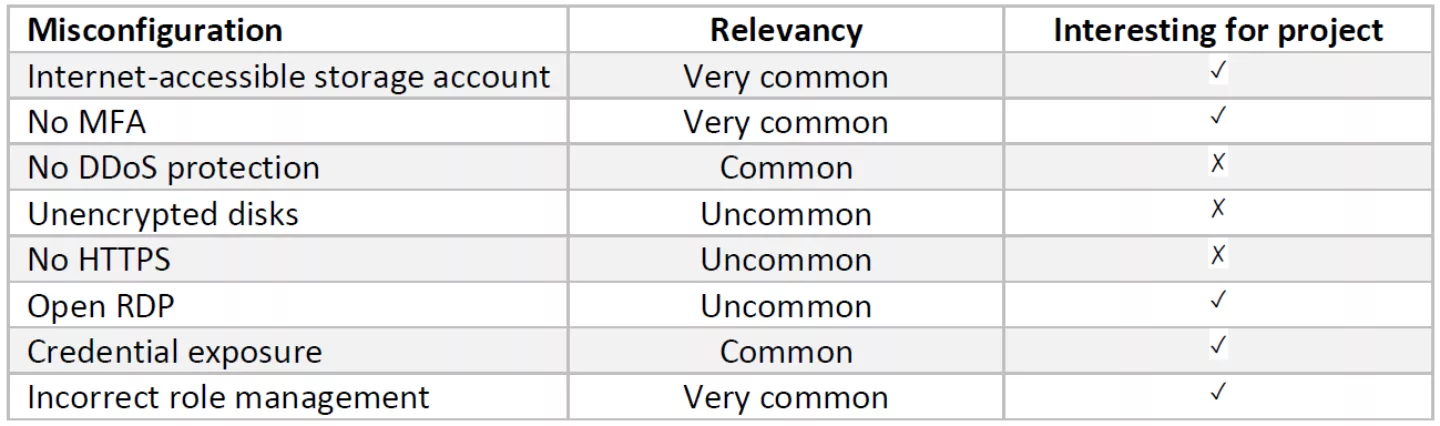
Table 1: Most Common Misconfigurations Azure Environments
Although all of these vulnerabilities are relevant, they are not useful to implement in a CTF challenge. A more specific research needed to be done on different attack surfaces that might be relevant to this project.
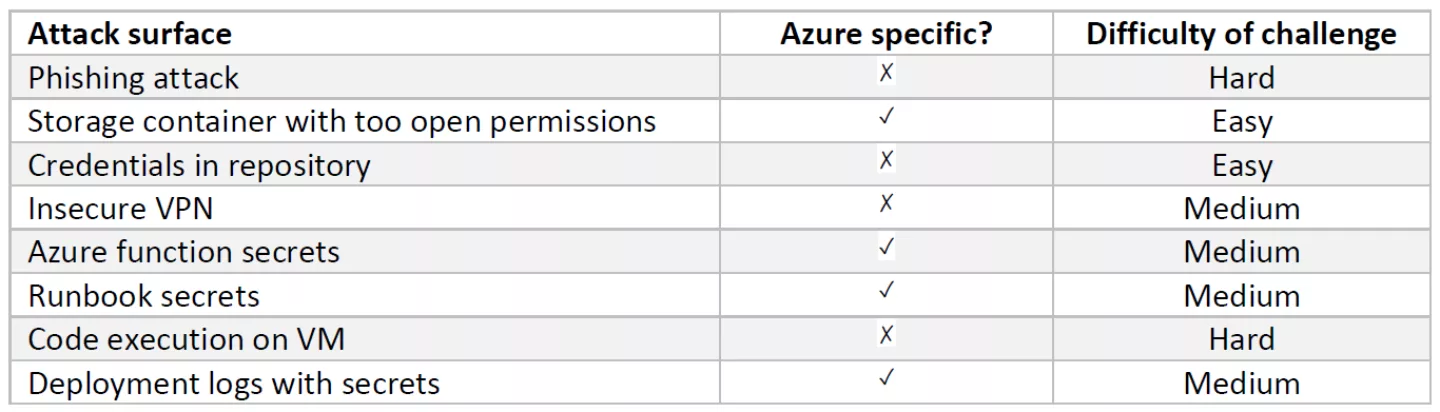
Table 2: Attack Surfaces
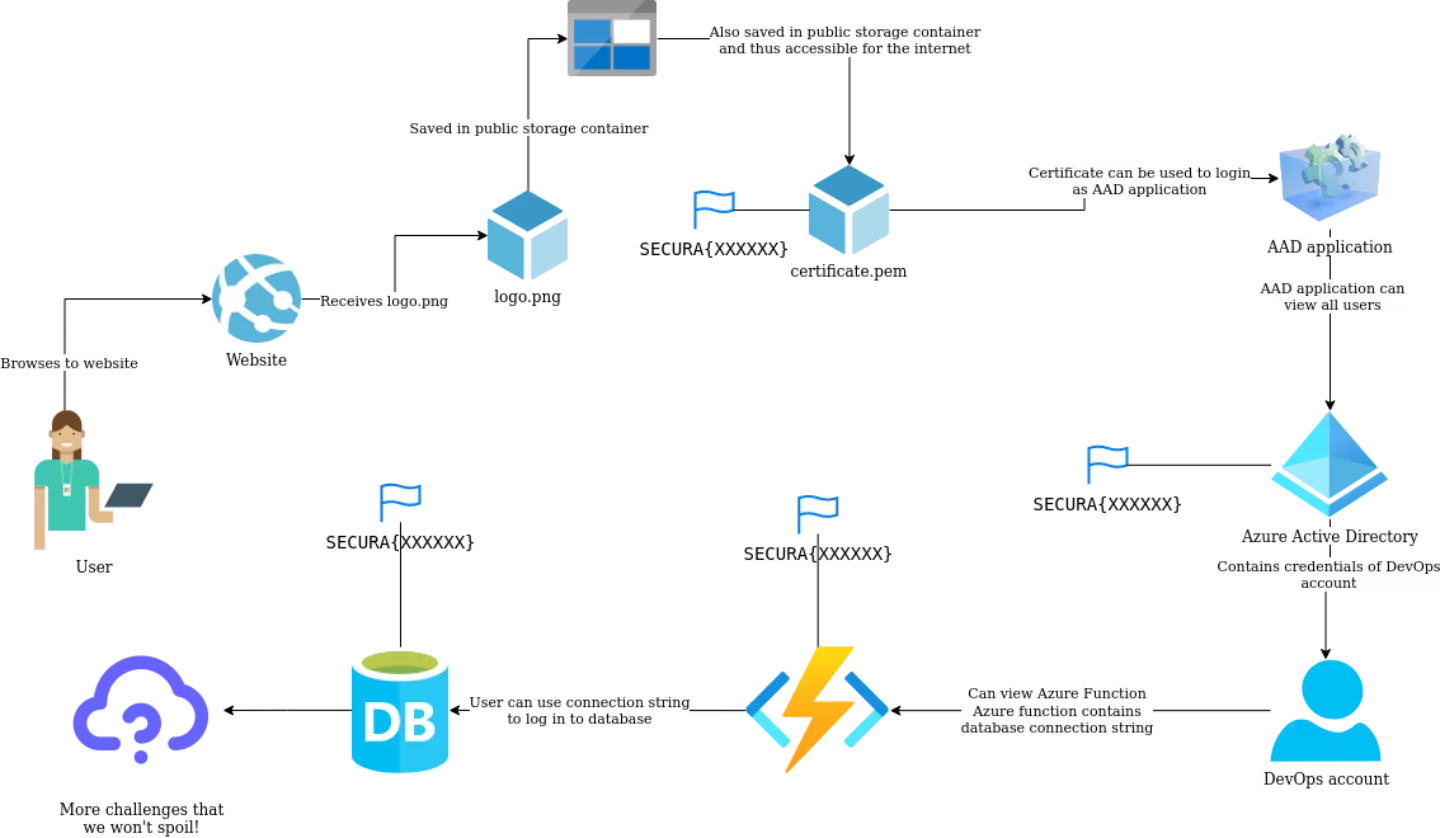
Based on these different attack surfaces, an Attack Chain has been created. This is the route that the hacker has to take to complete the capture the flag fully. Before entirely building the environment with Terraform, a diagram has been created to discuss the attack chain easily and have an overview of the environment.
The Final Result
As a result of this project, a CTF was created, which contains several challenges. The tool can be used by anyone with an interest in Azure hacking. Hints are available to guide you through the challenges and explain the underlying misconfigurations. Cloud experts are also invited to actively contribute to this project, to grow the challenges and robustness of the environment. Challenge yourself at BrokenAzure.Cloud or contribute at Github.
BrokenAzure.Cloud at DEF CON 2022
Because Ricardo Sanchez and Roy Stultiens were so enthusiastic about the final project, they decided that Siebren should submit the project to the DEF CON Village of Cloud. The talk has been accepted, and they will be speaking 13th of August at 13:10 PDT.
Future work
The software has a very robust base and can be used for training and recruiting purposes in its current state, but some future work can be done to make the tool even better. The tool can also be expanded with extra challenges, and different difficulties could be added.
This tool can be helpful for other companies apart from Secura. Because the tool is available online 24/7 (reset once per day), other companies can also use this tool for (internal) training and job application tests.
Cloud is changing rapidly, so the tool needs to be kept up-to-date with the newest changes in Azure and modify the challenges accordingly.
Some research can also be done on how the challenges might change the look on the cloud implementation of cloud- and network architects because this tool could also be used as a training tool for non-security specialists to learn about the risks of misconfigured cloud environments.
About Siebren and Roy
Siebren Kraak
Siebren is one of our security analysts that started working at Secura after successfully completing his internship assignment and graduating Cum Laude for his Bachelor of Science. In September he will start his master at the Radboud University where he will be specialising further in cyber security.
Roy Stultiens
Roy is one of our security specialists with 5+ years of DevOps experience. Starting off as a web developer focusing on back-end systems, architecture, and e-commerce he is now one of the experts in cloud security at Secura.
Do you have questions about the BrokenAzure.Cloud tool or our cloud security services? Feel free to contact us at info@secura.com or at +31 (0) 88 888 31 00.