NIS2 services to reach compliance
Need help with NIS2? Discover our expert services to help you meet the NIS2 cybersecurity requirements.
> Services with an integrated approach > NIS2
Get ready for NIS2
The urgency to comply with NIS2 is real. However, as an international cybersecurity company, we find that many organizations are falling behind in taking action. If you are uncertain about whether NIS2 applies to you, or where to start, let Secura help you.

Contact me about NIS2
Would you like to learn more about our NIS2 services for your organization? Please fill out the form and we will contact you within one business day.

Insight into gaps for NIS2
You gain insight into your current security controls and any gaps with NIS2 requirements.

A clear roadmap towards compliance
You receive a clear roadmap you can follow.

Help with implementation
You receive help implementing the measures you need to reach full NIS2 compliance.

NIS2 Boardroom Training
NIS2, the EU directive for Network & Information Security, aims to increase the cyber resilience of European companies and organizations across the entire supply chain.
Part of this directive is that directors can be personally liable if NIS2 is not complied with in their organization. Does your organization fall under NIS2? Then the law requires you to follow cybersecurity training as a director.
That's why we developed the one-day NIS2 Boardroom Training, together with De Clercq Lawyers. You will meet the NIS2 training requirements and receive a certificate.
What our customers say
We thought we had done most of the work for NIS2 already since we are ISO 27001 certified, so it came to us as a surprise that some of our more critical processes actually were not at all covered by our ISO certification. It's good that we found out about it in time.
YOUR NIS2 CHALLENGES
- To what extent do you already comply with NIS2?
- Which steps do you need to take to reach full compliance?
- Do you have the expertise to implement the measures needed for compliance?
- How are you going to train and prepare your staff for NIS2?
Don't underestimate the NIS2 law
If your organization already adheres to frameworks like ISO 27001, you might wonder how much further you have to go to meet the requirements of the NIS2 law. From experience we know, that most organizations still have to take extra steps. Conducting a gap analysis can be invaluable in identifying what you're already doing right and where additional measures are necessary.
The complexity of NIS2 shouldn't be underestimated. It is not a task that can be completed on a casual Friday afternoon. A hasty or uninformed approach not only leaves your organization vulnerable, but also puts you at risk of legal and financial penalties.
The implications of the NIS2 law extend all the way to the boardroom. Board members are now personally accountable for cybersecurity, making training more critical than ever. Ignoring or sidelining this training can lead to ineffective governance and, consequently, a failure to meet NIS2 requirements, which can result in severe legal repercussions.
NIS2 applies to many organizations
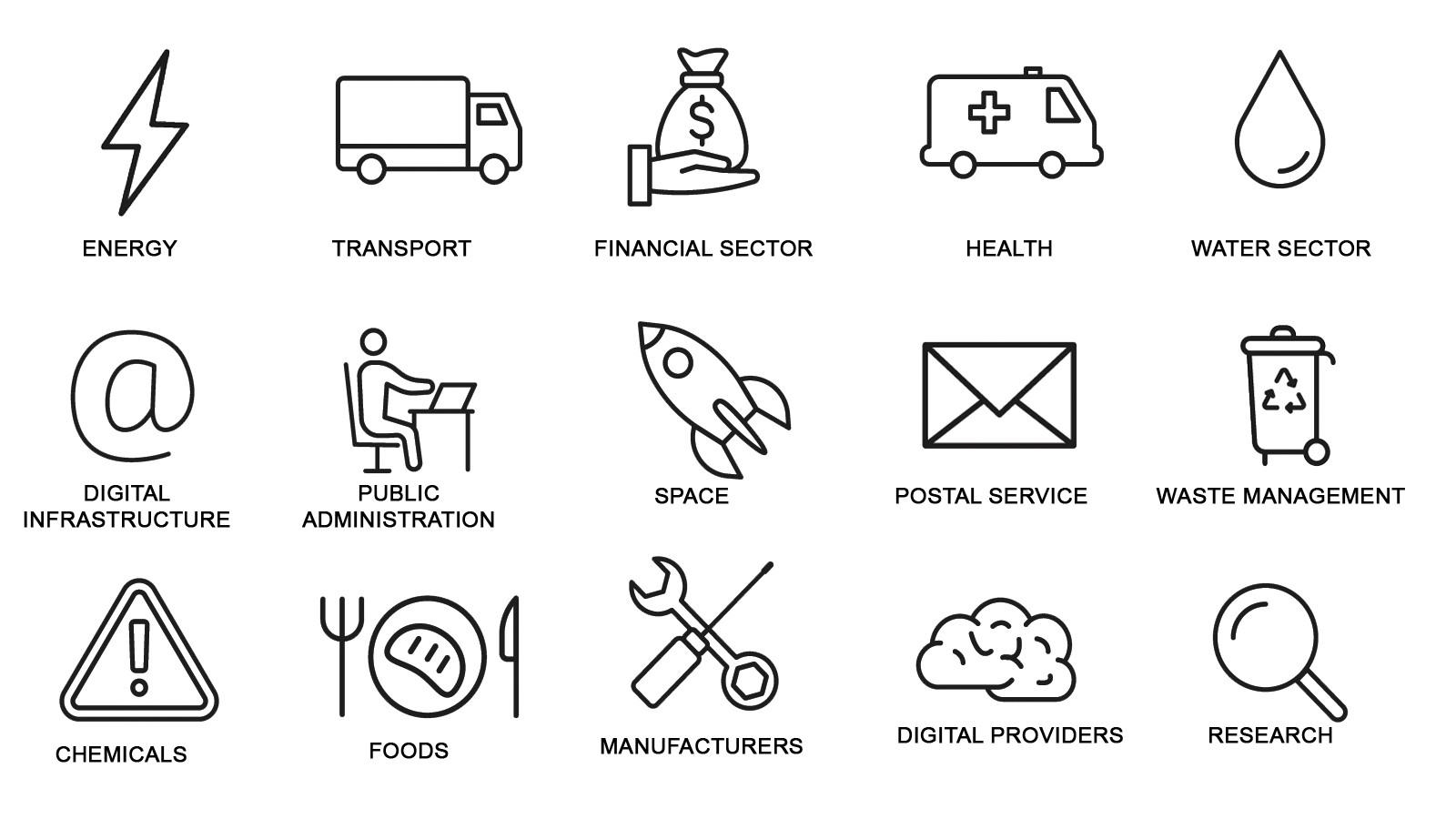
NIS2 applies to large and medium sized entities in these sectors
To Watch
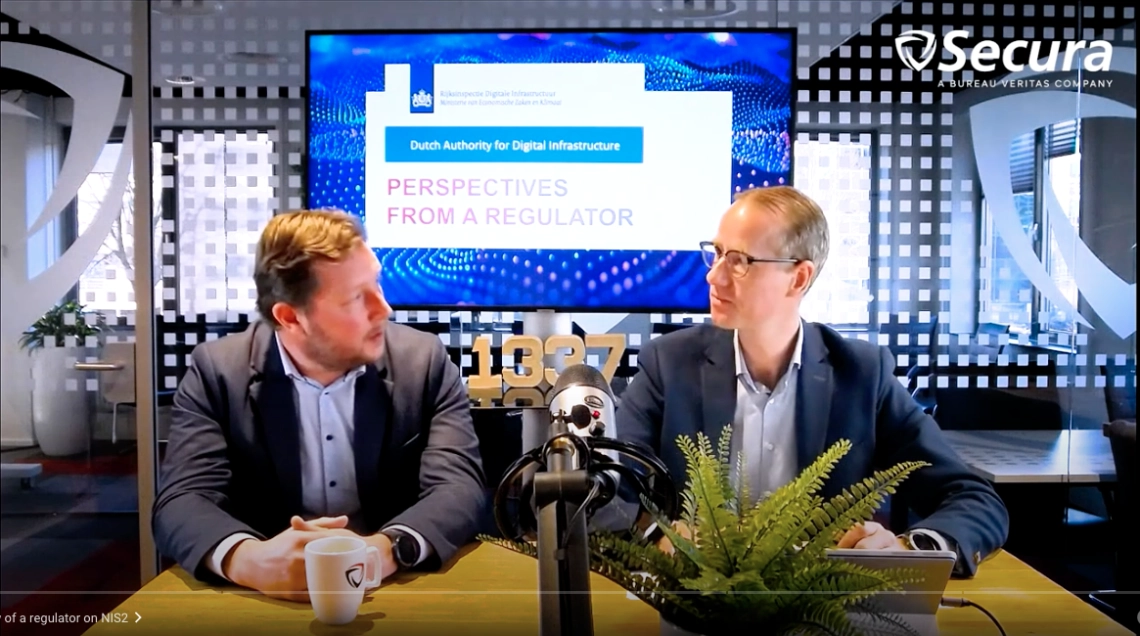
Webinar on Demand about the perspectives from a Regulator on NIS2
How does the Dutch National Inspectorate for Digital Infrastructure (formerly the Telecom Agency) view NIS2? Watch the replay of our webinar with Jasper Nagtegaal and Sjoerd Peerlkamp.
HOW WE SUPPORT YOU
Secura helps large and medium sized organizations all over Europe raise their cyber resilience. We know the importance of compliance to NIS2. Start preparing in time. Secura's NIS2 services help you to become NIS2 compliant. We offer the following NIS2 Services.
Frequently Asked Question: NIS2 Certification?
Currently, there is no official NIS2 certification, like the one you may know for ISO27001. However, there are local initiatives to enable certification, such as the NIS2 Quality Mark from Samenveilig.nl in the Netherlands, in which Secura is participating.
Steps towards NIS2 compliance
01
Verify if NIS2 applies to your organization
NIS2 applies to important and essential entities. Whether a company is so classified depends on the size and sector in which the company operates. We offer a free NIS2 Self Assessment here.
02
Train your board and staff
Training your employees, both at the boardroom level and other levels, is an essential part of NIS2. With the NIS2 Boardroom Training and SAFE Awareness Program, we can help you meet these requirements at all levels.
03
Map where your organization currently stands
To determine what steps you need to take to meet the requirements of the NIS2, it is important to have a good idea of what the security maturity levels of different parts of your organization currently are. The NIS2 Gap Assessment measures where you are and where you need to go. With this insight you know which steps you need to take to comply with NIS2.
04
Implement improvements
After determining where you stand and which steps are needed to meet the requirements of NIS2, it is time to implement measures. For example, CISO support or Incident Response services. Our broad range of services can support you both in the implementation and in the interpretation of measures.
05
NIS2 compliance
After completing these steps, you will be NIS2 compliant and your organization will be more secure in the face of cyber threats. Does this sound complicated? Then consider the CyberCare program, with which we support you throughout the process.
Download your ultimate NIS2 Guide
Discover your best next steps for NIS2. Please enter your name, email and company to download your NIS2 Guide immediately:
Benefits of Secura's NIS2 Services
Decades of governance risk and compliance experience
A range of services specifically developed to meet your NIS2 needs and help you become NIS2 compliant
Cybersecurity experts in the field of People, Process and Technology
A clear roadmap to become and stay NIS2 compliant

NIS2: Who Does It Apply To?
Who is the NIS2 law applicable to? To what sectors? Does it apply to your company or organization? Take the NIS2 Self-Assessment (1-5 minutes) to determine if your company or organization is classified as essential or important:
MORE INFORMATION
Would you like to learn more about our NIS2 Services? Please fill out the form, and we will contact you within one business day.

Why choose Secura | Bureau Veritas
At Secura/Bureau Veritas, we are dedicated to being your trusted partner in cybersecurity. We go beyond quick fixes and isolated services. Our integrated approach makes sure that every aspect of your company or organization is cyber resilient, from your technology to your processes and your people.
Secura is the cybersecurity division of Bureau Veritas, specialized in testing, inspection and certification. Bureau Veritas was founded in 1828, has over 80.000 employees and is active in 140 countries.












